0x00 写在前面
从零学习php,最终目的实现代码审计入门,软件采用sublime text,环境使用phpstudy搭建,数据库是navicat,需要有基本的前端基础、简单的php+mysql后端基础、渗透知识和漏洞原理,文章跟随流沙前辈学习记录,看看曾经遥不可及的代码审计能不能慢慢啃下来。
本章为代码审计入门第五篇-DVWA靶场篇,对DVWA靶场漏洞进行代码审计。
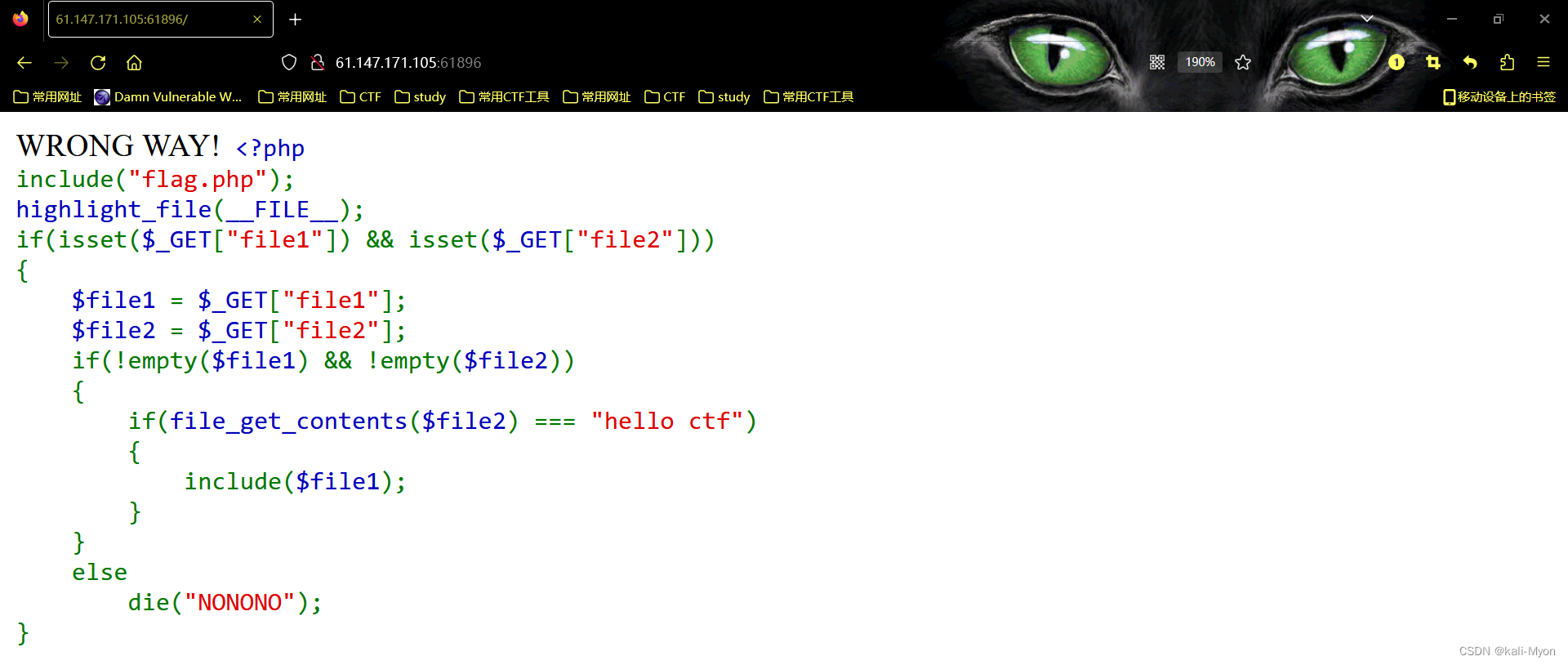
0x01 暴力破解
暴力破解模块,注释写在代码里,尽量用详细的语言描述代码含义。
level-low
存在万能密码,可绕过用户名
low.php
<?phpif( isset( $_GET[ 'Login' ] ) ) { //isset函数检测变量非空且设置
// Get username
$user = $_GET[ 'username' ]; //GET方式接收用户名 // Get password
$pass = $_GET[ 'password' ]; //GET方式接收密码
$pass = md5( $pass ); //接收到的密码进行md5加密 // Check the database
$query = "SELECT * FROM `users` WHERE user = '$user' AND password = '$pass';";
//直接交互数据库,用户名存在万能密码 /*var_dump($query); //这里可以添加var_dump输出代码进行调式
exit();*/ $result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
//直接将SQL语句的执行结果显示给客户端
if( $result && mysqli_num_rows( $result ) == 1 ) {
//mysqli_num_rows()接受一个结果对象作为参数,检索返回给定结果的行数。实践见下图 // Get users details
$row = mysqli_fetch_assoc( $result );
//取一行比对
$avatar = $row["avatar"]; // Login successful
$html .= "<p>Welcome to the password protected area {$user}</p>";
$html .= "<img src=\"{$avatar}\" />";
//成功输出xxx调用图片
}
else {
// Login failed
$html .= "<pre><br />Username and/or password incorrect.</pre>";
} ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}?>
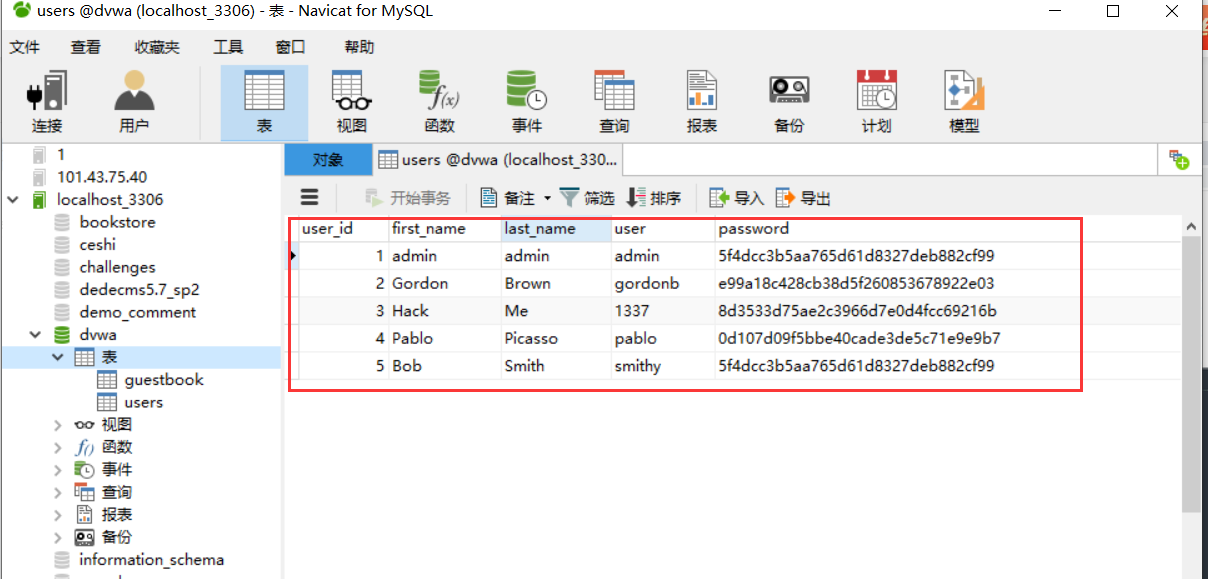
//为什么可以爆破,因为没用作任何限制数据库users表单是五行数据,使用mysqli_num_rows()返回总共的行数

初级基本就这么多了
level-medium
这里相较于low,最大的区别点在于使用mysqli_real_escape_string()函数进行转义以防止恶意注入,所以万能密码登陆用不了了。
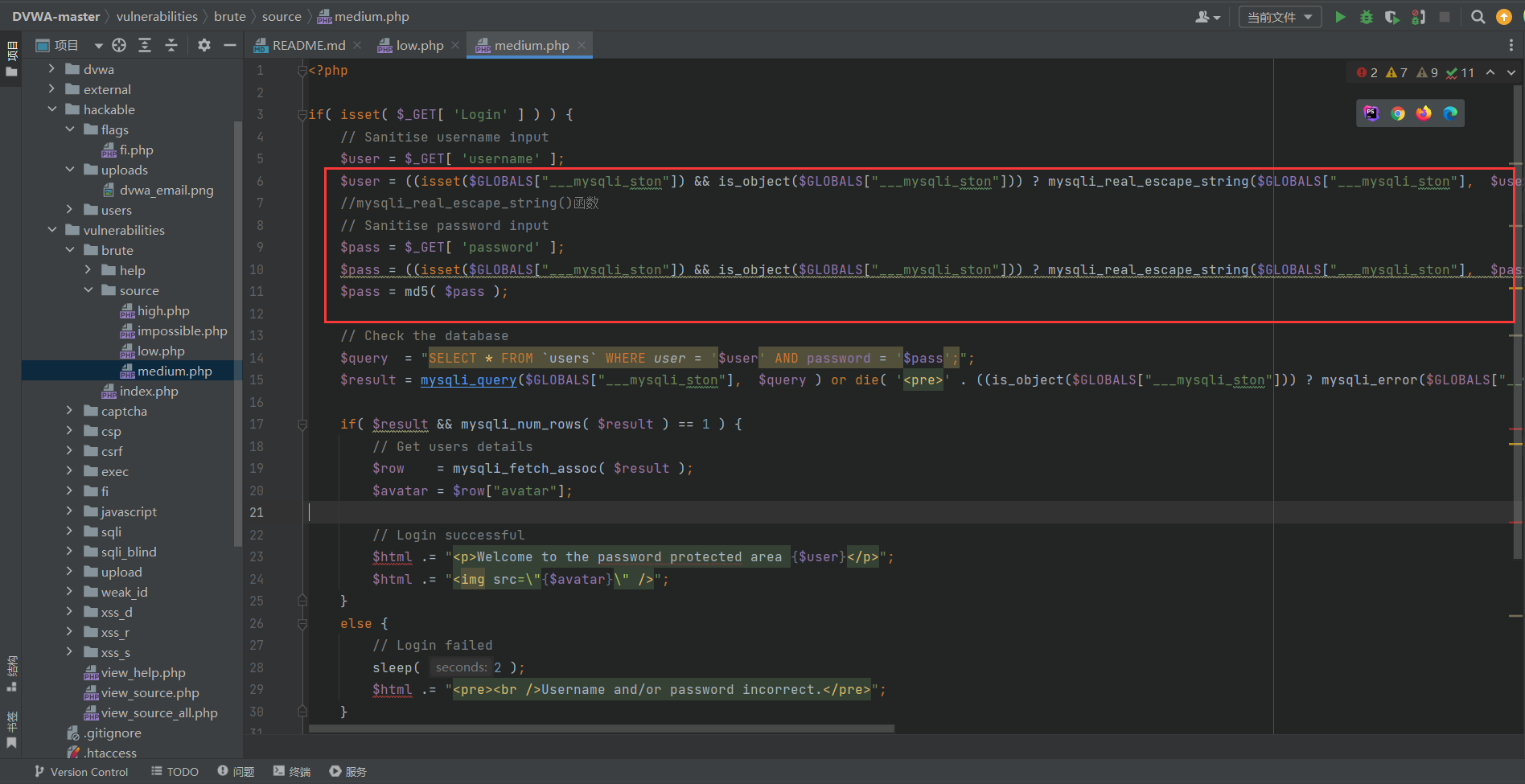
但有可能存在宽字节绕过,这与本身使用的php版本有关,可参考之前文章的第三十六关:
SQLI-labs靶场Less1-37详细学习记录(7400字总结)_身高两米不到的博客-CSDN博客

level-high
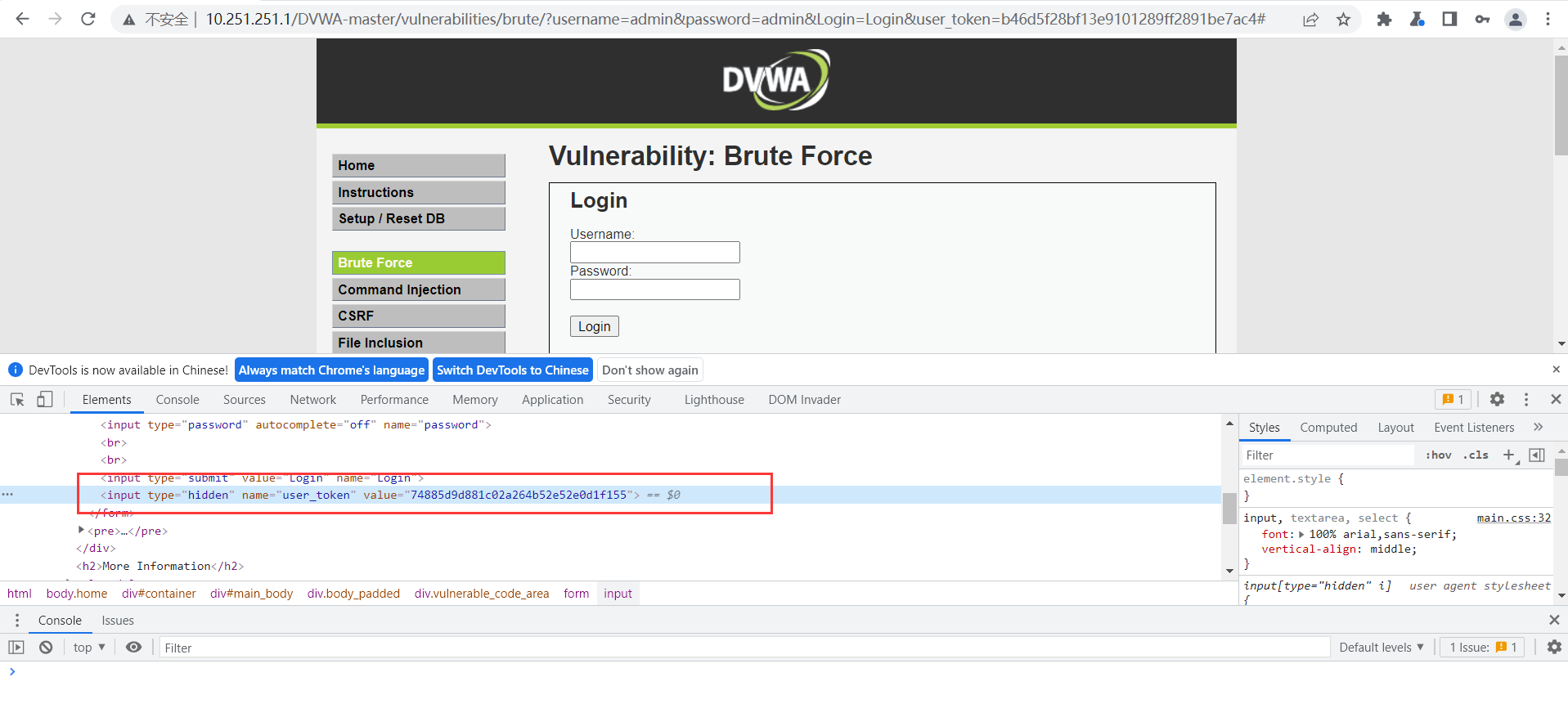
high和之前相比最大的区别点在于token认证
high.php
<?phpif( isset( $_GET[ 'Login' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
//调用checkToken
// Sanitise username input
$user = $_GET[ 'username' ];
$user = stripslashes( $user ); //删除反斜杠,防注入的
$user = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $user ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : "")); // Sanitise password input
$pass = $_GET[ 'password' ];
$pass = stripslashes( $pass );
$pass = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$pass = md5( $pass ); // Check database
$query = "SELECT * FROM `users` WHERE user = '$user' AND password = '$pass';";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' ); if( $result && mysqli_num_rows( $result ) == 1 ) {
// Get users details
$row = mysqli_fetch_assoc( $result );
$avatar = $row["avatar"]; // Login successful
$html .= "<p>Welcome to the password protected area {$user}</p>";
$html .= "<img src=\"{$avatar}\" />";
}
else {
// Login failed
sleep( rand( 0, 3 ) );
//随机slep0-3秒
$html .= "<pre><br />Username and/or password incorrect.</pre>";
} ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}// Generate Anti-CSRF token
generateSessionToken();?>
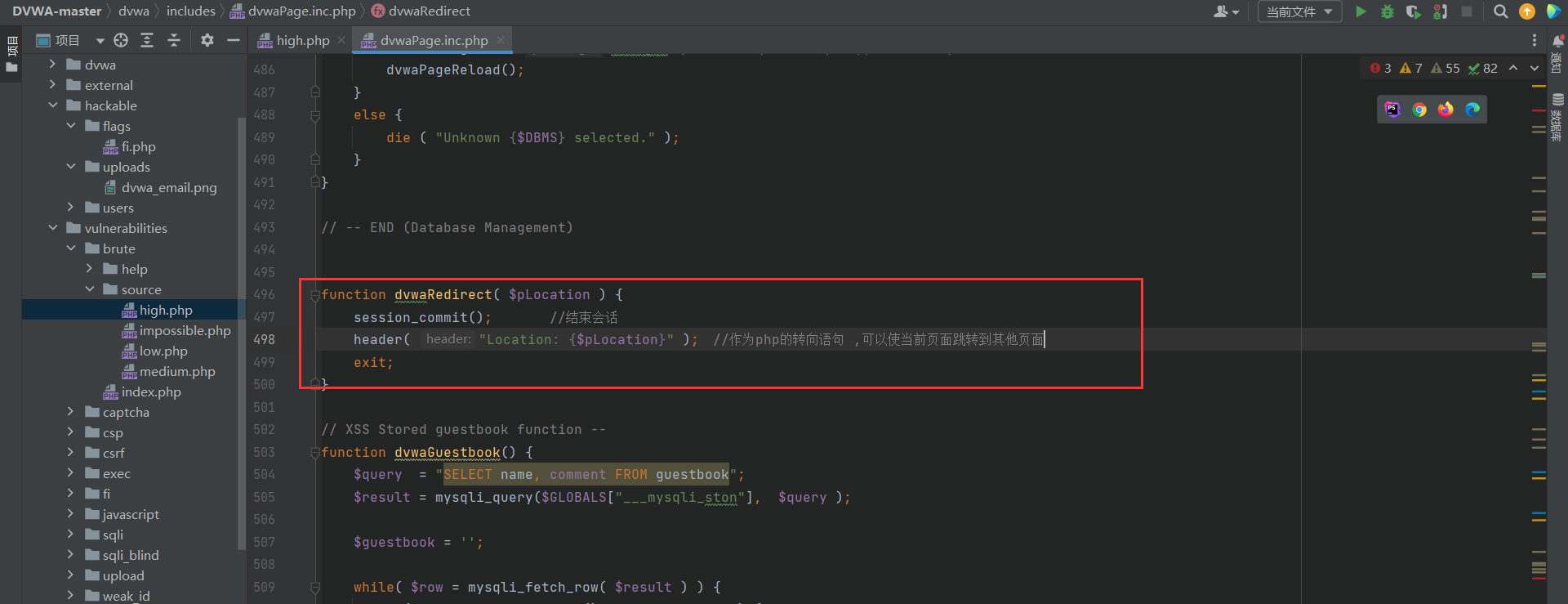
跟进到checkToken方法,设置三个参数,如果user_token不等于session_token或者session_token为空,调用dvwaRedirect方法。
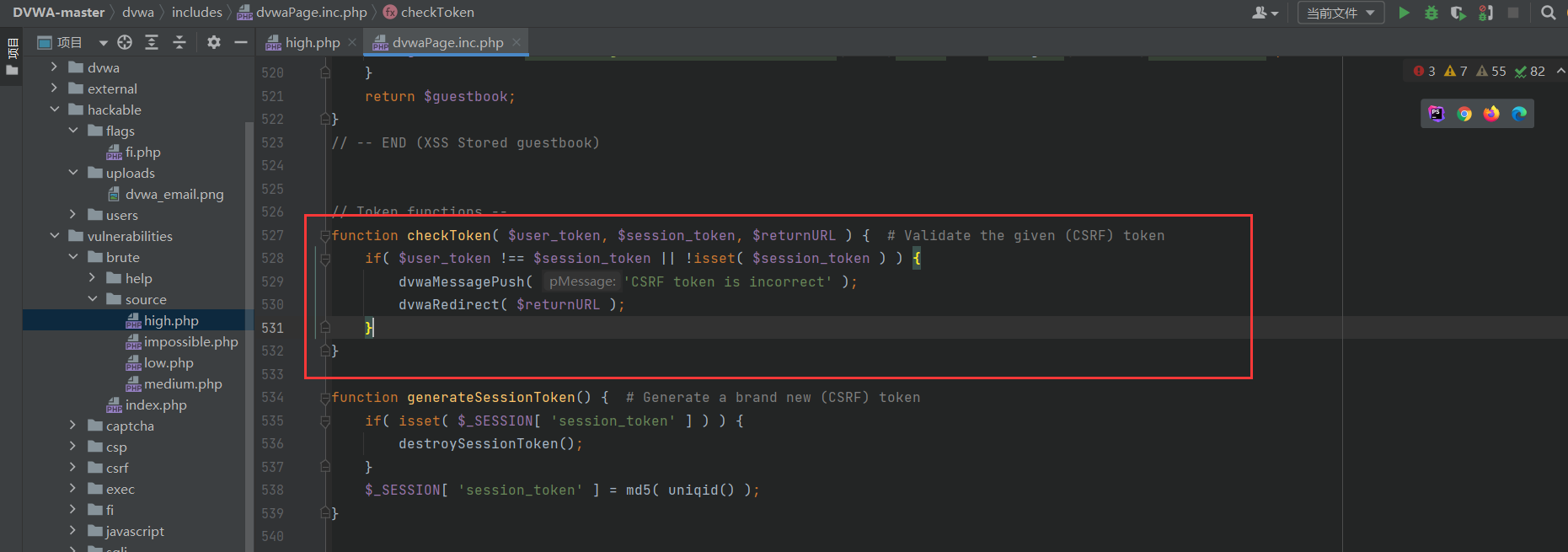
跟进到dvwaRedirect,发现起到跳转作用
F12可以查看随机生成的token,token爆破绕过可以参考之前文章
level-impossiable
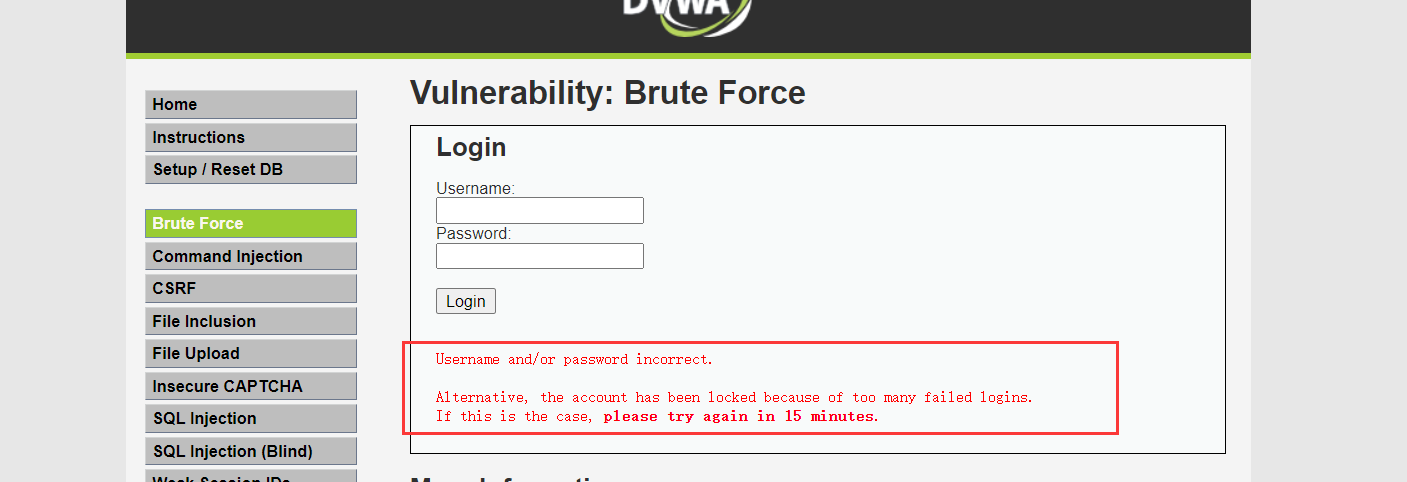
既然是impossibale,那以咱水平肯定绕不过去,直接看代码,代码对防注入方面使用了PDO预处理,对于爆破而言最狗的是设置次数。实际目标站点渗透可以死猜个用户名,然后弱密码隔断时间试试,至于hw还是早点溜了。
impossiable.php
<?phpif( isset( $_POST[ 'Login' ] ) && isset ($_POST['username']) && isset ($_POST['password']) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' ); // Sanitise username input
$user = $_POST[ 'username' ]; //改成POST提交账号密码
$user = stripslashes( $user );
$user = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $user ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : "")); // Sanitise password input
$pass = $_POST[ 'password' ];
$pass = stripslashes( $pass );
$pass = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$pass = md5( $pass );
//前面还是token,以及防注入的函数使用 // Default values
$total_failed_login = 3; //登陆次数失败三次
$lockout_time = 15; //等十五分钟
$account_locked = false; //判断用户是否锁定 // Check the database (Check user information)
$data = $db->prepare( 'SELECT failed_login, last_login FROM users WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
//使用PDO
$data->execute();
$row = $data->fetch(); // Check to see if the user has been locked out.
if( ( $data->rowCount() == 1 ) && ( $row[ 'failed_login' ] >= $total_failed_login ) ) {
// User locked out. Note, using this method would allow for user enumeration!
//$html .= "<pre><br />This account has been locked due to too many incorrect logins.</pre>"; // Calculate when the user would be allowed to login again
$last_login = strtotime( $row[ 'last_login' ] );
$timeout = $last_login + ($lockout_time * 60);
$timenow = time(); /*
print "The last login was: " . date ("h:i:s", $last_login) . "<br />";
print "The timenow is: " . date ("h:i:s", $timenow) . "<br />";
print "The timeout is: " . date ("h:i:s", $timeout) . "<br />";
*/ // Check to see if enough time has passed, if it hasn't locked the account
if( $timenow < $timeout ) {
$account_locked = true;
// print "The account is locked<br />";
}
} // Check the database (if username matches the password)
$data = $db->prepare( 'SELECT * FROM users WHERE user = (:user) AND password = (:password) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR);
$data->bindParam( ':password', $pass, PDO::PARAM_STR );
$data->execute();
$row = $data->fetch(); // If its a valid login...
if( ( $data->rowCount() == 1 ) && ( $account_locked == false ) ) {
// Get users details
$avatar = $row[ 'avatar' ];
$failed_login = $row[ 'failed_login' ];
$last_login = $row[ 'last_login' ]; // Login successful
$html .= "<p>Welcome to the password protected area <em>{$user}</em></p>";
$html .= "<img src=\"{$avatar}\" />"; // Had the account been locked out since last login?
if( $failed_login >= $total_failed_login ) {
$html .= "<p><em>Warning</em>: Someone might of been brute forcing your account.</p>";
$html .= "<p>Number of login attempts: <em>{$failed_login}</em>.<br />Last login attempt was at: <em>${last_login}</em>.</p>";
} // Reset bad login count
$data = $db->prepare( 'UPDATE users SET failed_login = "0" WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
} else {
// Login failed
sleep( rand( 2, 4 ) ); // Give the user some feedback
$html .= "<pre><br />Username and/or password incorrect.<br /><br/>Alternative, the account has been locked because of too many failed logins.<br />If this is the case, <em>please try again in {$lockout_time} minutes</em>.</pre>"; // Update bad login count
$data = $db->prepare( 'UPDATE users SET failed_login = (failed_login + 1) WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
} // Set the last login time
$data = $db->prepare( 'UPDATE users SET last_login = now() WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
}// Generate Anti-CSRF token
generateSessionToken();?>
关于PDO预编译防注入原理推荐文章:
奇安信攻防社区-SQL注入&预编译
0x02 总结
工作一年多重回校园,以打工人身份又转变到学生,这段时间开始忙碌,没有办法,作业考试太多。。。




发表评论 取消回复